Sensors | Free Full-Text | Research on Security Weakness Using Penetration Testing in a Distributed Firewall
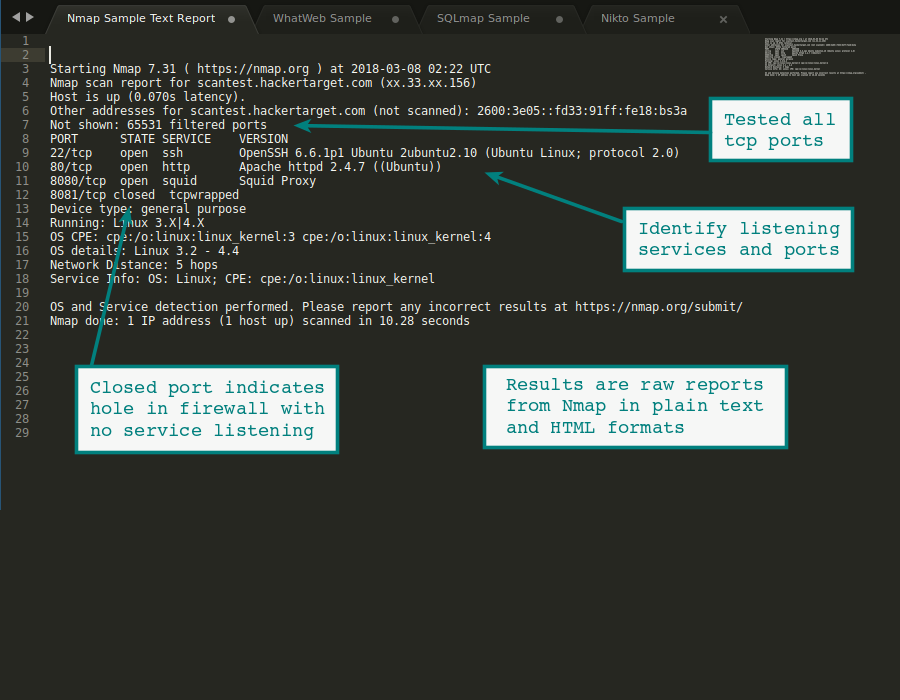
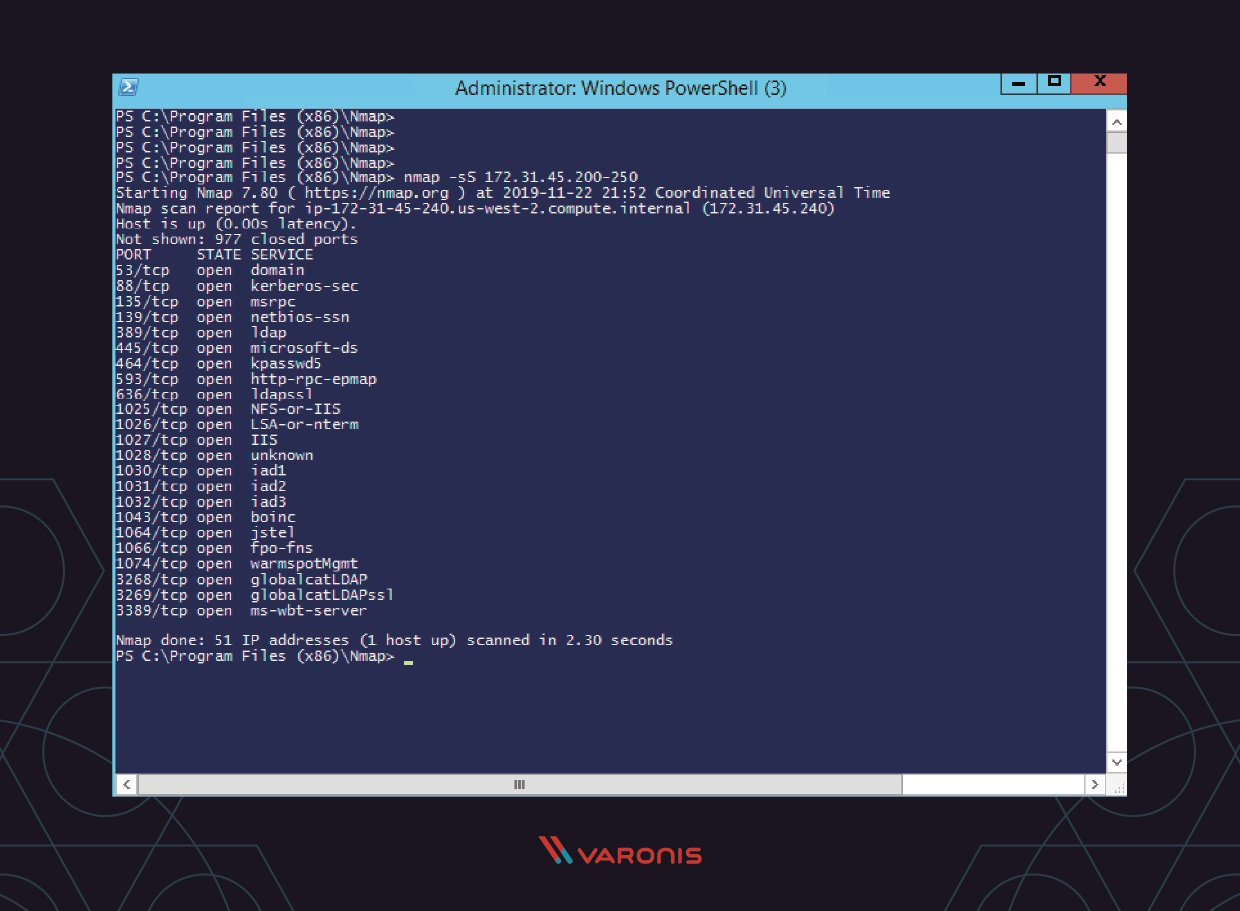
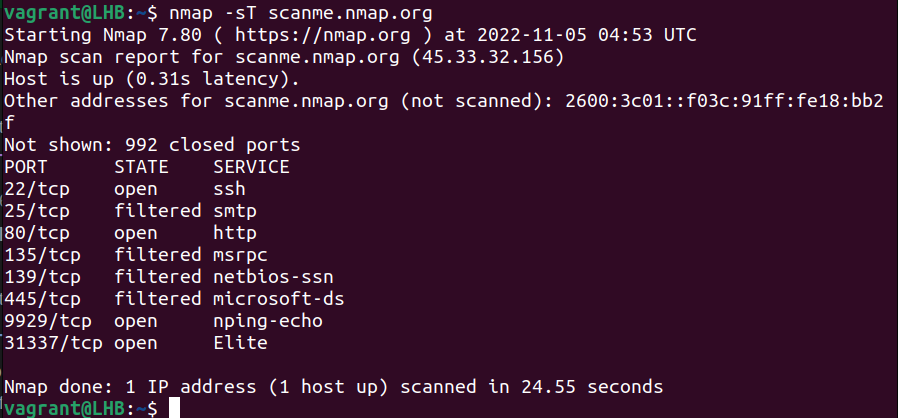
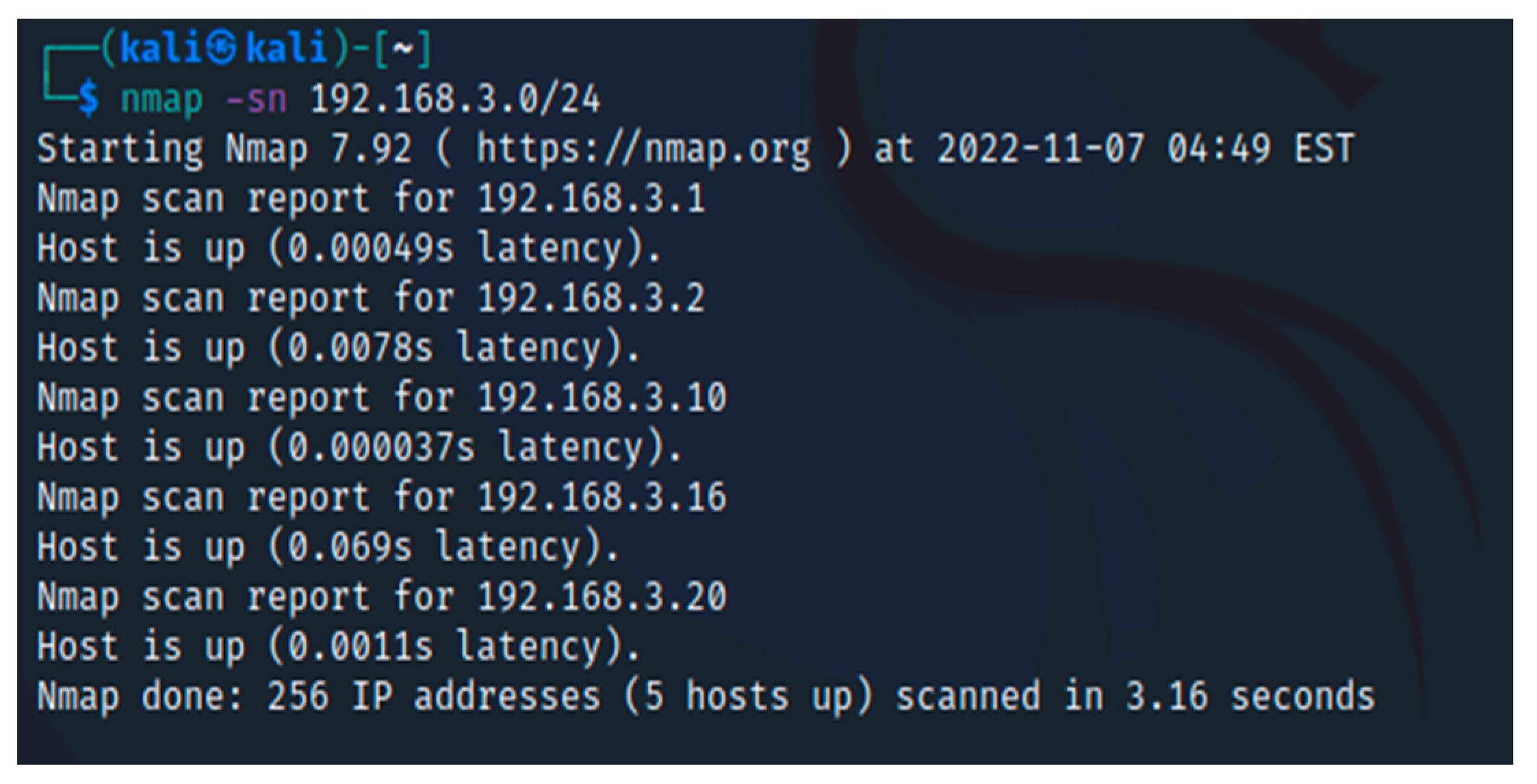
Optimizing Your Nmap Scan: Nmap Scanning Methods - Professor Messer IT Certification Training Courses

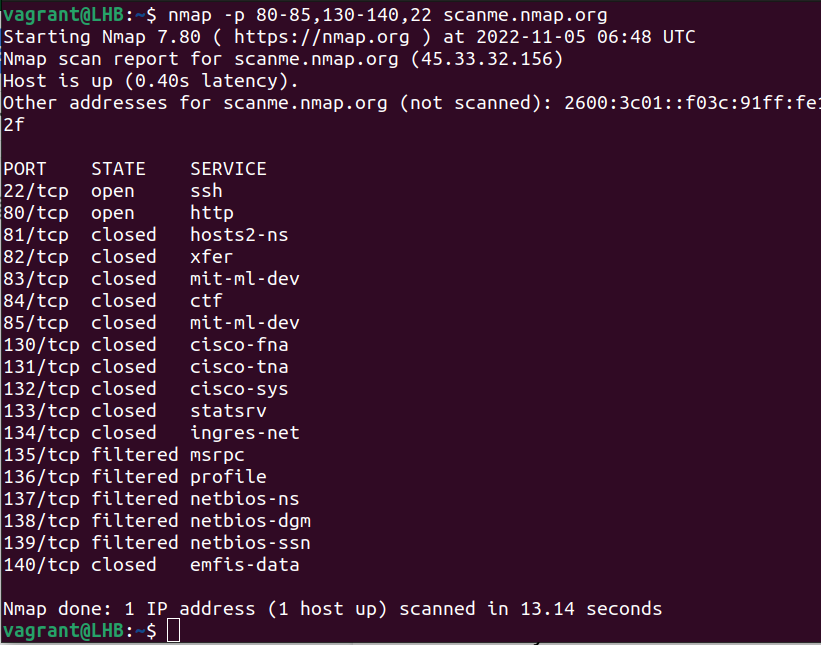
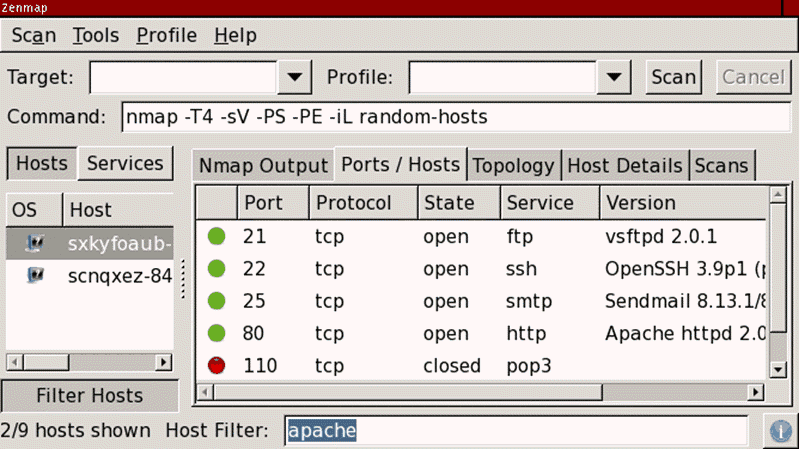
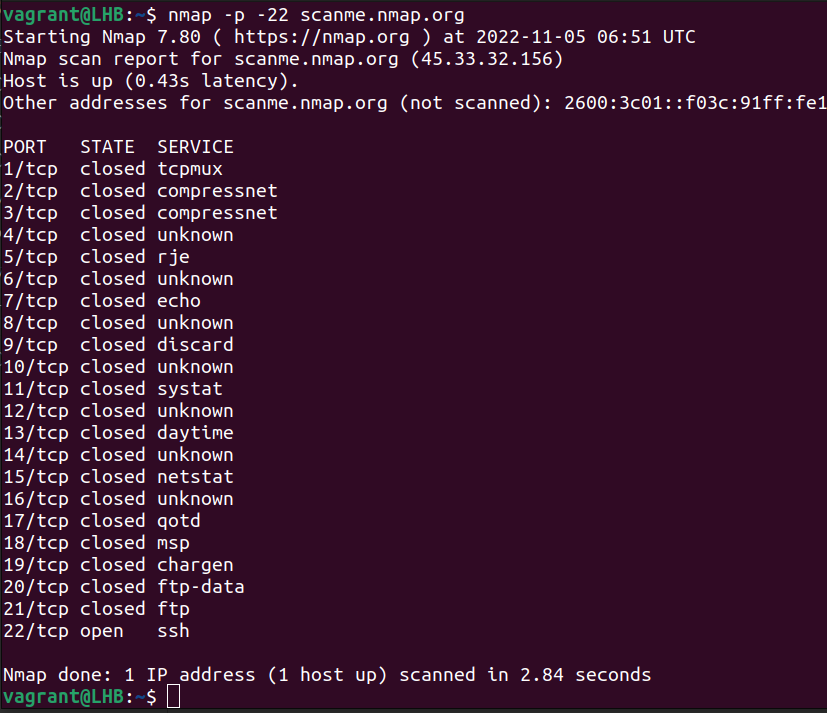
Nmap cheat sheet: From discovery to exploits, part 2: Advance port scanning with Nmap and custom idle scan | Infosec Resources